What is Fuzzing? Why it is Important on Cybersecurity?
What is Fuzzing?
Fuzz testing or Fuzzing is a Black Box software testing technique, which basically consists in finding implementation bugs using malformed/semi-malformed data injection in an automated task.
This analysis is a software-testing technique used by developers and penetration testers to test their applications against unexpected, invalid, and random sets of data input. The response will then be noticed in terms of an exception or a crash thrown by the application. This activity shows us some of the major vulnerabilities in the application, which are not possible to discover otherwise. These covers buffer overflows, format strings, code injections, dangling pointers, race conditions, denial of service conditions, and many other types of vulnerabilities.
Fuzzy analysis is a relatively simple and effective solution that can be incorporated into the quality assurance and security testing processes. That’s why fuzzy analysis is also called robustness testing or negative testing sometimes.
History of Fuzzing
Classic fuzz testing was developed at the University of Wisconsin Madison in 1989 by Professor Barton Miller and students. Their (continued) work can be found here. It’s mostly oriented towards command-line and UI fuzzing, and shows that modern operating systems are vulnerable to even simple fuzzing.
Attack types in Fuzzing
Commonly a Fuzzer (program for fuzzing) would try combinations of attacks on:
- numbers (signed/unsigned integers/float etc).
- chars (urls, command-line inputs).
- metadata : user-input text (id3 tag).
- pure binary sequences.
A common approach to fuzzing is to define lists of “known-to-be-dangerous values” (fuzz vectors) for each type, and to inject them or re-combinations.
- For integers: zero, possibly negative or very big numbers.
- For chars: escaped, interpretable characters / instructions (ex: For SQL Requests, quotes / commands etc).
- For binary: random ones.
- For chars: escaped, interpretable characters / instructions (ex: For SQL Requests, quotes / commands etc).
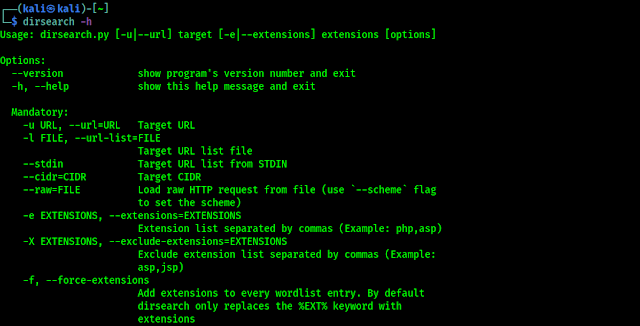
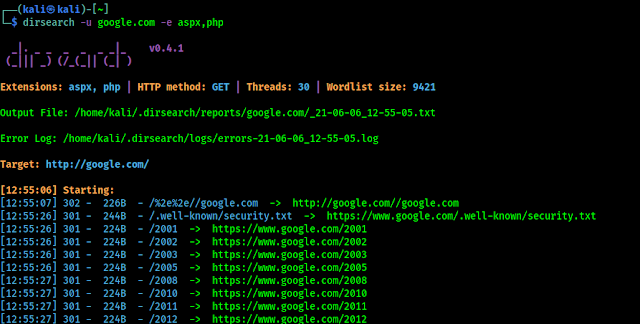
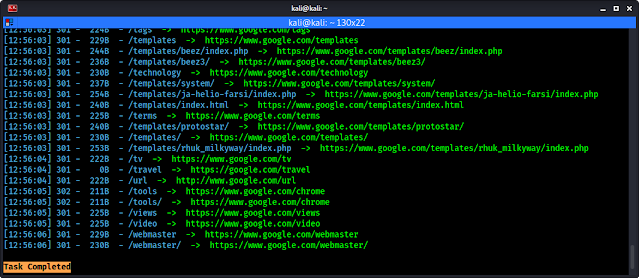
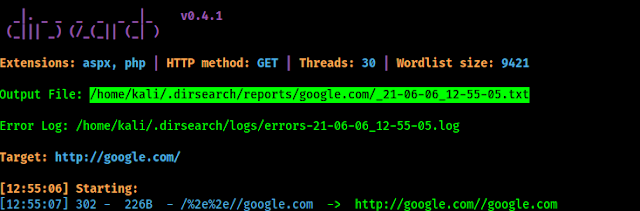
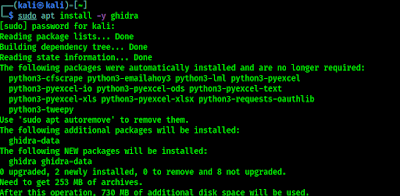
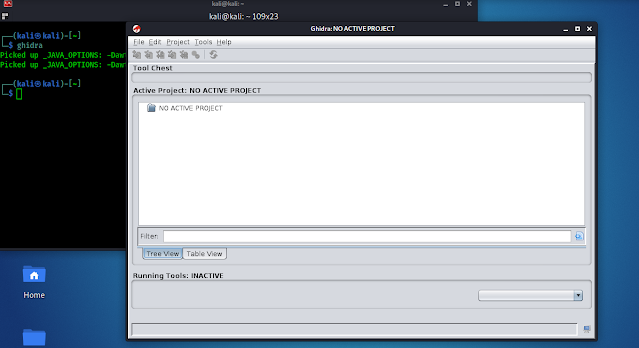
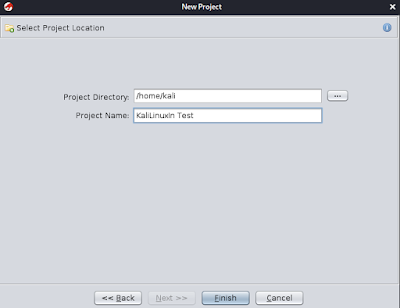
There are different classes of fuzzers available in Kali Linux, which can be used to test the file formats, network protocols, command-line inputs, environmental variables, and web applications. Any non-trusted source of data input is considered to be insecure and inconsistent. For instance, a trust boundary between the application and the Internet user is unpredictable. Thus, all the data inputs should be fuzzed and verified against known and unknown vulnerabilities. In our some later article we are going to learn about Fuzzers on our Kali Linux system.
Why Fuzzing is important on Security Testing?
The purpose of fuzzing based on the assumption that there are bugs within every program, which are waiting to be discovered. Then, a systematic approach should find them sooner or later.
Fuzzing can add another perspective to classical software testing techniques (hand code review, debugging) because of it is non-human approach. It doesn’t replace them, but is a reasonable complement, thanks to the limited work needed to put the procedure in place.
References
- Wikipedia Article.
- Fuzzing-related papers.
- The fuzzing mailing list archive.
- OWASP community Article.
Love our articles? Make sure to follow us on Twitter and GitHub, we post article updates there. To join our KaliLinuxIn family, join our Telegram Group. We are trying to build a community for Linux and Cybersecurity. For anything we always happy to help everyone on the comment section. As we know our comment section is always open to everyone. We read each and every comment and we always reply.




























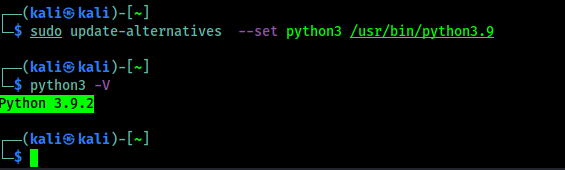
![Set Default Version of Python : [SOLVED] update-alternatives: error: no alternatives for python3 Set Default Version of Python : [SOLVED] update-alternatives: error: no alternatives for python3](https://infocerts.com/wp-content/uploads/2021/07/Default-Version-of-Python-infocerts.jpg)