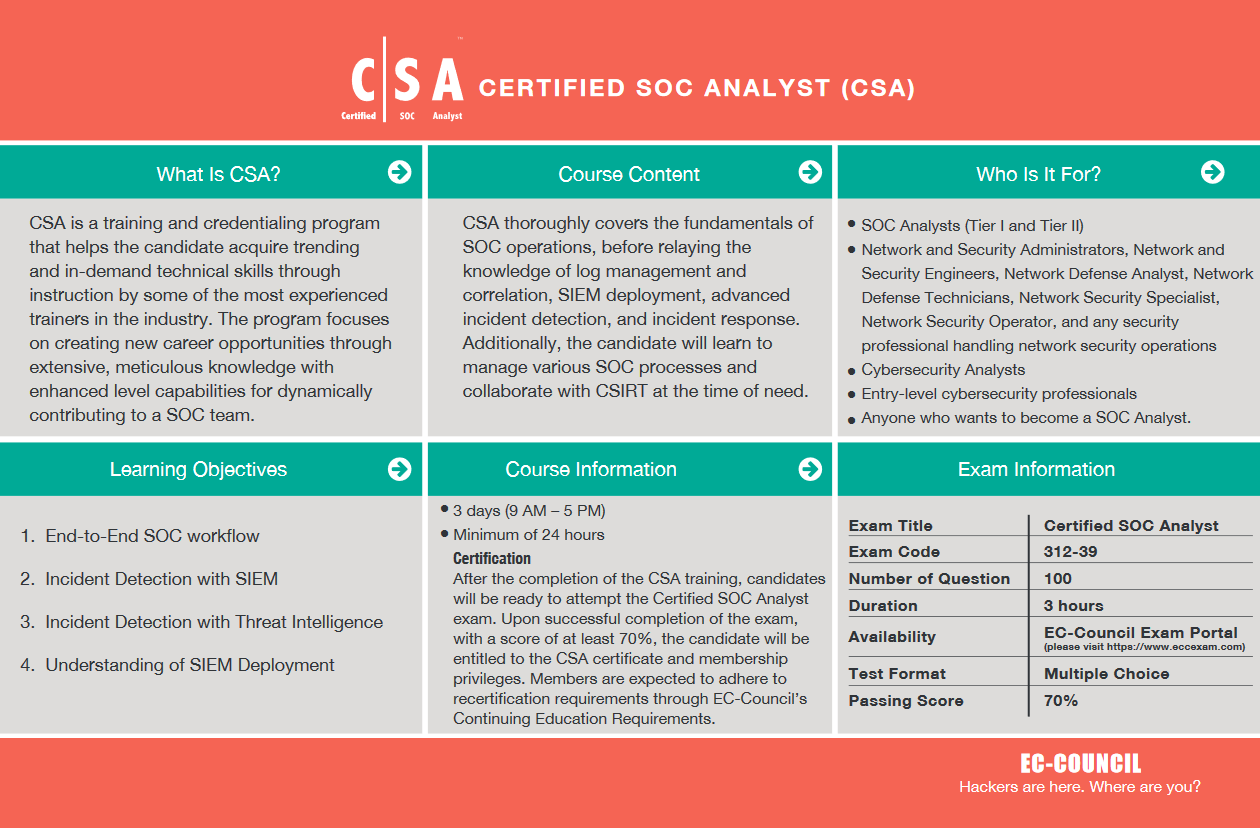
EC-Council CERTIFIED SOC ANALYST (CSA) 312-39
As the security landscape is expanding, a SOC team offers high-quality IT-security services to detect potential cyber threats/attacks actively and quickly respond to security incidents. Organizations need skilled SOC Analysts who can serve as the front-line defenders, warning other professionals of emerging and present cyber threats.
The lab-intensive SOC Analyst training program emphasizes the holistic approach to deliver elementary as well as advanced knowledge of how to identify and validate intrusion attempts. Through this, the candidate will learn to use SIEM solutions and predictive capabilities using threat intelligence. The program also introduces the practical aspect of SIEM using advanced and the most frequently used tools. The candidate will learn to perform enhanced threat detection using the predictive capabilities of Threat Intelligence.
Duration
24 Hours | 3 Days
Fri-Sat-Sun
Training Cost
Exam
EC-Council CEH Exam (312-39)
Duration: 3hrs | Questions: 100
Brochure
Certification By

Jobs related to SOC
CSA Objectives
Gain Knowledge of SOC processes, procedures, technologies, and workflows.
Gain basic understanding and in-depth knowledge of security threats, attacks, vulnerabilities,
attacker’s behaviors, cyber kill chain, etc.
Able to recognize attacker tools, tactics, and procedures to identify indicators of compromise
(IOCs) that can be utilized during active and future investigations.
Able to monitor and analyze logs and alerts from a variety of different technologies across
multiple platforms (IDS/IPS, end-point protection, servers and workstations).
Gain knowledge of Centralized Log Management (CLM) process.
Able to perform Security events and log collection, monitoring, and analysis.
Gain experience and extensive knowledge of Security Information and Event Management.
Gain knowledge on administering SIEM solutions (Splunk/AlienVault/OSSIM/ELK).
Understand the architecture, implementation and fine tuning of SIEM solutions (Splunk/
AlienVault/OSSIM/ELK).
Gain hands-on experience on SIEM use case development process.
Able to develop threat cases (correlation rules), create reports, etc.
Learn use cases that are widely used across the SIEM deployment.
Plan, organize, and perform threat monitoring and analysis in the enterprise.
Able to monitor emerging threat patterns and perform security threat analysis.
Gain hands-on experience in alert triaging process.
Able to escalate incidents to appropriate teams for additional assistance.
Able to use a Service Desk ticketing system.
Able to prepare briefings and reports of analysis methodology and results.
Gain knowledge of integrating threat intelligence into SIEM for enhanced incident detection
and response.
Able to make use of varied, disparate, constantly changing threat information.
Gain knowledge of Incident Response Process.
Gain understating of SOC and IRT collaboration for better incident response.
Course Outline
Module 1 – Security Operations and Management
Module 2 – Understanding Cyber Threats, IoCs, and Attack Methodology
Module 3 – Incidents, Events, and Logging
Module 4 – Incident Detection with Security Information and Event Management (SIEM)
Module 5 – Enhanced Incident Detection with Threat Intelligence
Module 6 – Incident Response
Who Should Attend
The CSA program requires a candidate to have 1 year of work experience
in the Network Admin/ Security domain and should be able to provide
proof of the same as validated through the application process unless
the candidate attends official training.
Job Roles
- SOC Analysts (Tier I and Tier II)
- Network and Security Administrators,
- Network and Security Engineers,
- Network and Security Specialist,
- Network and Security Operator,
- Cybersecurity Analyst, and.
- entry-level cybersecurity professionals.
About the Training & Exam
The CSA exam is designed to test and validate a candidate’s comprehensive understanding of the jobs tasks required as a SOC analyst. Thereby validating their comprehensive understanding of a complete SOC workflow
Exam Title :- Certified SOC Analyst
Exam Code :- 312-39
Number of Questions :- 100
Duration :- 3 hours
Availability :- EC-Council Exam Portal (please visit https://www. eccexam.com)
Test Format :- Multiple Choice
Passing Score :- 70%
How can we help?
Sample Certificate
Latest Blog Post
Cybersecurity and Cloud Computing
INTRODUCTION: The cloud offers unparalleled flexibility, scalability, and cost-effectiveness, enabling...
Read MoreCategories of Security Challenges in Cloud Computing – Other concerns
This article is about security challenges in cloud computing with...
Read MoreCategories of Security Challenges in Cloud Computing – Backup and Recovery issues
Backup and Recovery issues Backup (B1) Cloud Computing servers are...
Read MoreCategories of Security Challenges in Cloud Computing – Confidentiality and Privacy
This article says about Confidentiality and Privacy, one type of...
Read More