August 28, 2021
WAScan – Web Application Scanner is a Open Source web application security scanner. It is designed to find various vulnerabilities using “black-box” method, that means it won’t study the source code of web applications but will work like a fuzzer, scanning the pages of the deployed web application .
WAScan is built on python2.7 and can run on any platform which has a Python environment.
WAScan Attacks
- Bash Commands Injection
- Blind SQL Injection
- Buffer Overflow
- Carriage Return Line Feed
- SQL Injection in Headers
- XSS in Headers
- HTML Injection
- LDAP Injection
- Local File Inclusion
- OS Commanding
- PHP Code Injection
- SQL Injection
- Server Side Injection
- XPath Injection
- Cross Site Scripting
- XML External Entity
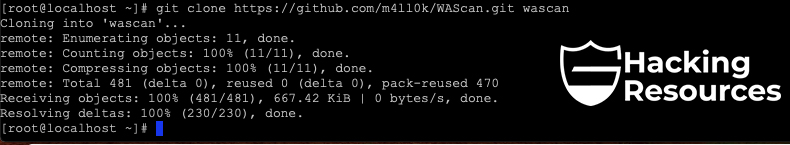
Installation WAScan :
$ git clone https://github.com/m4ll0k/WAScan.git wascan
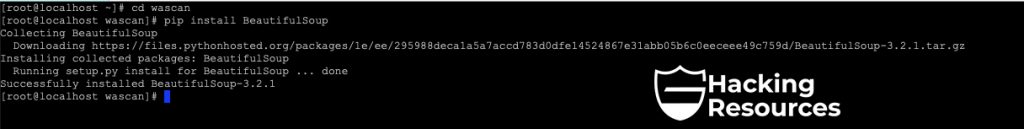
$ cd wascan
$ pip install BeautifulSoup
$ python wascan.py

Usage WAScan
$ python wascan.py --url http://xxxxx.com/ --scan 0
Attacks:
$ python wascan.py --url http://xxxxx.com/index.php?id=1 --scan 1
Advanced Usage :
$ python wascan.py --url http://xxxxx.com/test.php --scan 5 --auth "admin:1234"
$ python wascan.py --url http://xxxxx.com/test.php --scan 5 --data "id=1" --method POST
$ python wascan.py --url http://xxxxx.com/test.php --scan 5 --auth "admin:1234" --proxy xxx.xxx.xxx.xxx
$ python wascan.py --url http://xxxxx.com/test.php --scan 5 --auth "admin:1234" --proxy xxx.xxx.xxx.xxx --proxy-auth "root:4321"
$ python wascan.py --url http://xxxxx.com/test.php --scan 5 --auth "admin:1234" --proxy xxx.xxx.xxx.xxx --proxy-auth "root:4321 --ragent -vArticle posted by: https://hackingresources.com/wascan-web-application-scanner/
——————————————————————————————————————–
Infocerts, 5B 306 Riverside Greens, Panvel, Raigad 410206 Maharashtra, India
Contact us – https://www.infocerts.com

