A quick summary of the change log since the 2021.1 release from February 2021 is:
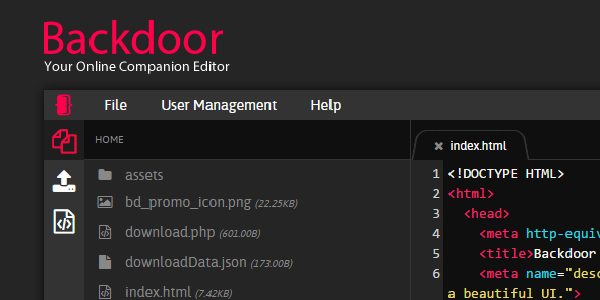
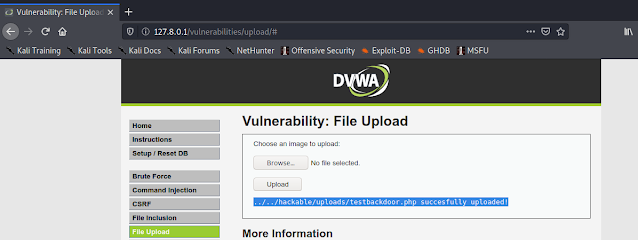
Introducing Kaboxer v1.0
For developers, this is a great new tool in the arsenal. Users will, hopefully, not realise that they are using it, only noticing that previously problematic tools now work correctly!
Without repeating what has already been posted, this technology allows us to correctly package up programs that were previously difficult, with items such as complex dependencies or legacy programs & libraries (such as Python 2 or dated SSL/TLS).
With Kaboxer’s launch, we have released 3 packages using it:
If you want to read more, please see either our blog post covering it, or our documentation around it.
Kaboxer is still in its infancy, so please be nice & patient with it.
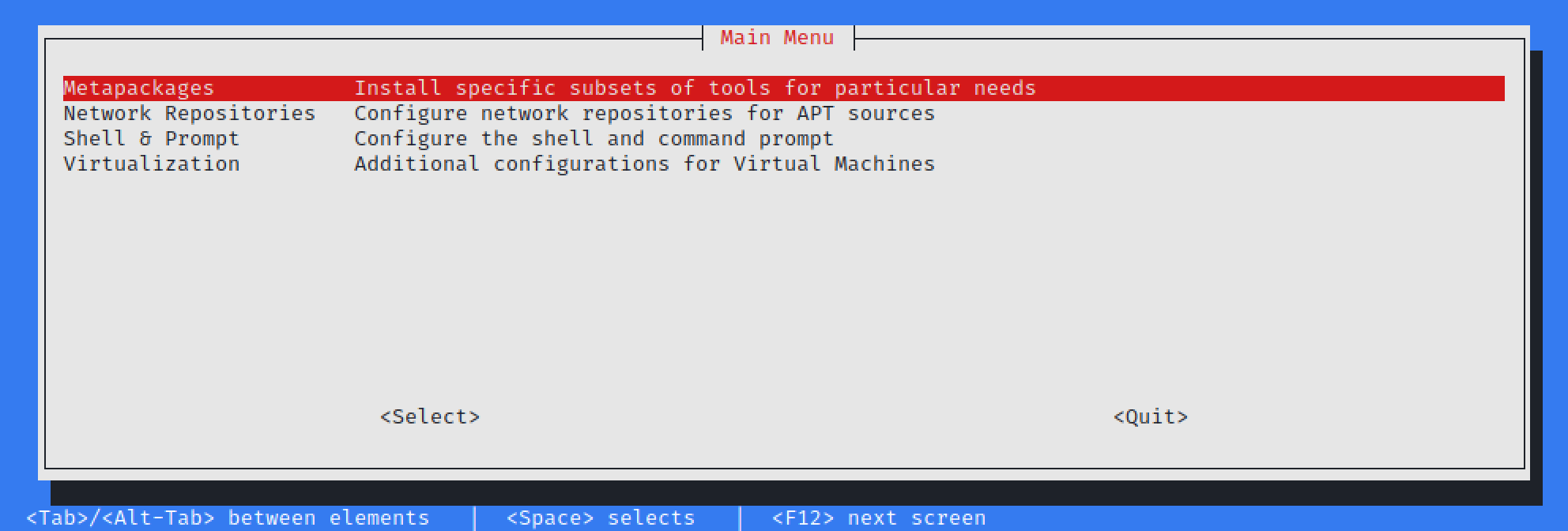
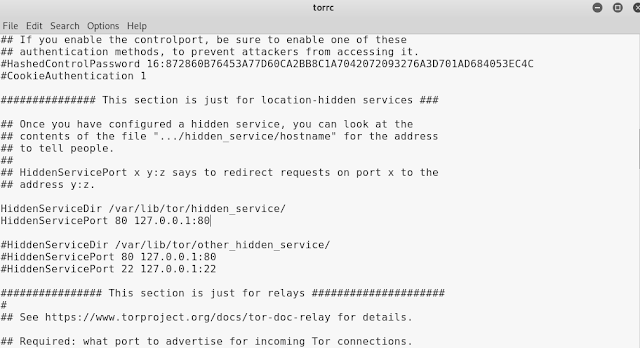
Releasing Kali-Tweaks v1.0
Announcing Kali-Tweaks! This is our little helping hand for Kali users, with the idea to help customize Kali to your own personal taste quickly, simply, and the correct way. This should help you to stop doing repetitive tasks.
Currently Kali-Tweaks will help out with:
- Metapackages – Installing/removing groups of tools, which may not have been available while installing Kali if you did not use the installer image
- Network Repositories – Enabling/disabling “bleeding-edge” & “experimental” branches
- Shell & Prompt – Switch between two or one line prompt, enable/disable the extra line before the prompt, or configure Bash or ZSH as the default shell
- Virtualization – Using Kali as a guest VM? Do a few actions to make the experience easier!
Our philosophy is to always understand what you are running, before you run it. That way, it reduces the chances of any undesirable nasty surprises. Which is why we will always encourage anyone to do actions manually before automating it, so you get to understand what is happening under the hood. On the flip side, we also understand there is so much to remember. Then when you sprinkle in people’s bad habits, which often have long term implications and end up breaking Kali, there is room for improvement. So, we started developing Kali-Tweaks. Where possible, Kali-Tweaks will also display what commands are being executed to help educate users.
We do want to mention a few things:
kali-tweaks has been marked as “recommended” rather than “required”. As a result, if you are upgrading Kali, it may not be included. On the other hand, you can remove kali-tweaks without removing anything else- On the subject of upgrading; depending on how old your Kali installation is, you may need to reset your shell resource (e.g.
.bashrc & .zshrc) before you can use the “configure prompt” section. This is because it will not have the necessary variables. Should you want to, make sure to backup, reset, and restore
- The last thing to point out, when changing the default login shell; please log out and in again (either graphically or remote console) for it to have an effect
It is still early days with Kali-Tweaks, and we already have ideas of what to expand into, but we welcome any suggestions from you!
Kali-Tweaks is still in its infancy, so please be nice & patient with it.
Refreshed Bleeding-Edge Branch
Kali’s Bleeding-Edge branch has been around since March 2013, but we have recently completely restructured the backend.
For those not too familiar with Bleeding-Edge branch, here is a breakdown:
- Kali by default opts to be stable where possible when packaging. This means some tools may appear to be “out-dated”
- We do this by looking to see when the tool author(s) signals “everything up to to this point is good”, by doing a “point release” (e.g.
1.0 or 2.1)
- Developers often use source-code version control, allowing them to track any changes
- How programmers use source-code version control depends on their work flow, experience, and team size
- Developers can use a “tag” feature found in most source-code version control to signal when there is a new version (this is what Kali prefers)
- However, some people may say if it makes it to “master” or “main” branch, then it is “production ready”
- There are times where it has been “a while” (months or even years) since doing a tag for a stable release (aka point release), and people get frustrated that there are no updates (e.g. hashcat or impacket).
You may then end up skipping the Kali package and compiling your favorite tool’s source-code. This might then conflict with Kali’s packaging, and it is your responsibility to maintain the program. This is where bleeding-edge branch comes in.
Since moving over to GitLab, we have been able to create Kali-Bot to help with heavy lifting and automation
- Automatically package tag’d releases to kali-experimental branch
- Automatically package the last commit to kali-bleeding-edge branch
This is a fully automated procedure, as a result, the testing that goes into our packaging is automated as well (unlike anything that is in kali-rolling branch which has manual testing involved). If there has not been a unit test created, its not going to be tested for. This means there is a chance packages will be broken, and more trust goes into the tool author having correctly developed the tool.
If you want to give it a try, have a look at our kali-bleeding-edge documentation to learn how to enable the repository and how to tell apt to select a package from this repository. Once the repository has been enabled, it looks like this:
kali@kali:~$ dpkg -l
| grep ffuf
ii ffuf 1.3.1-0kali1 amd64
Fast web fuzzer written in Go (program)
kali@kali:~$
kali@kali:~$ sudo apt install -y ffuf/kali-bleeding-edge
...
kali@kali:~$
kali@kali:~$ dpkg -l
| grep ffuf
ii ffuf 1.3.1+git20210505.1.f032167-0kali1~jan+nus1 amd64
Fast web fuzzer written in Go (program)
kali@kali:~$
Not every tool has made it to the new system yet as there are still many limitations to overcome, but to see what is supported and also how many:
kali@kali:~$ curl -s -L 'http://http.kali.org/kali/dists/kali-bleeding-edge/main/binary-amd64
/Packages'
| awk -F ': ' '/^Package: /{print $2}'
...
kali@kali:~$
kali@kali:~$ curl -s -L 'http://http.kali.org/kali/dists/kali-bleeding-edge/main/binary-amd64/
Packages'
| awk -F ': ' '/^Package: /{print $2}'
| wc -l
78
kali@kali:~$
kali@kali:~$ curl -s -L 'http://http.kali.org/kali/dists/kali-experimental/main/binary-amd64/
Packages'
| awk -F ': ' '/^Package: /{print $2}'
| wc -l
192
kali@kali:~$
kali@kali:~$ curl -s -L 'http://http.kali.org/kali/dists/kali-rolling/main/binary-amd64/
Packages'
| awk -F ': ' '/^Package: /{print $2}'
| wc -l
59518
kali@kali:~$
The numbers will only grow bigger and better as time goes on, with less bugs in the code and more unit tests in place!
If you are a tool author and want to get your software on the list, please chat to us, and we can show how to enable webhooks!
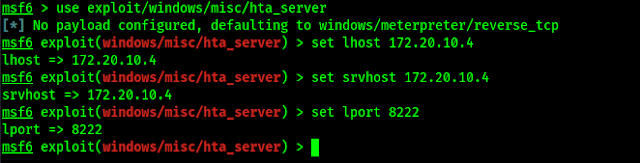
Disabled Privileged Ports
We have patched our kernel to remove the restriction of requiring privilege permission in order to use TCP & UDP ports under 1024 (meaning 0/TCP-UDP <= 1023/TCP-UDP). This was done because:
- We see Kali as a desktop OS, rather than a server
- This “well-known” privileged port range is reserved for server services (e.g. 80/TCP HTTP, 443/TCP HTTPS)
- With the switch from Kali’s root to non-root user by default, rather than doing a port forward from outside the privilege ports to a restricted port, people were just running the program with super-user permissions instead
- We get it. It’s quicker to run:
$ sudo <program>,
- Rather than remembering something like:
$ sudo iptables -A PREROUTING -t nat -i eth0 -p tcp --dport 80 -j REDIRECT --to-port 8888
- It also can get complex and confusing with a lot of redirects setup in place
- Alternatively people were using
authbind to allow certain users to use certain ports
- This defeats the point of switching to non-root user!
- Let’s reduce any possible attack surface!
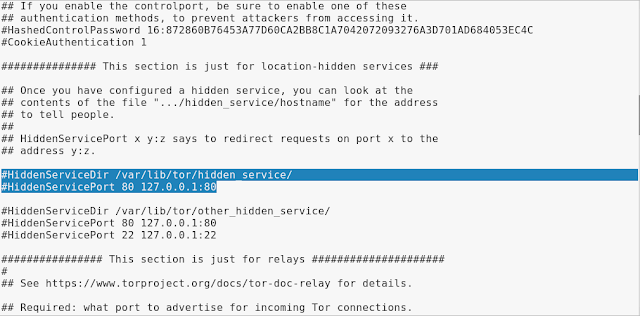
Now, this change won’t appear in all instances as some flavors of Kali operate without our kernel. This depends on which platform you use (such as Cloud instances, Docker or WSL). If you are on a platform that does not use our customized Kernel, this change will not be applied. For example, the top one uses Kali’s kernel on a bare metal install, and below uses Kali in a docker container, so its using the host’s kernel:
kali@kali:~$ uname -r
5.10.0-kali7-amd64
kali@kali:~$
...vs...
$ docker run --rm --interactive --tty kalilinux/kali:latest uname -r
5.10.25-linuxkit
$
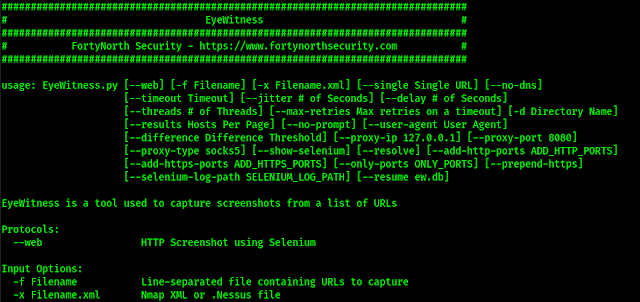
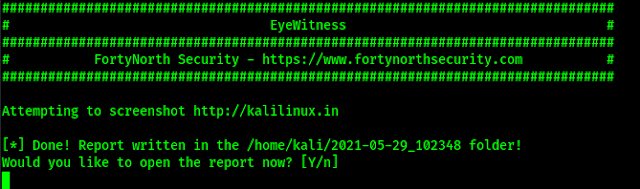
It would not be a Kali release if there were not any new tools added! A quick run down of what’s been added (to Kali’s archive and network repositories):
- CloudBrute – Find a company infrastructure, files, and apps on the top cloud providers
- Dirsearch – Brute force directories and files in web servers
- Feroxbuster – Simple, fast, recursive content discovery
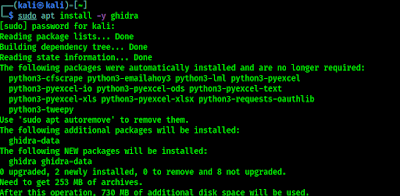
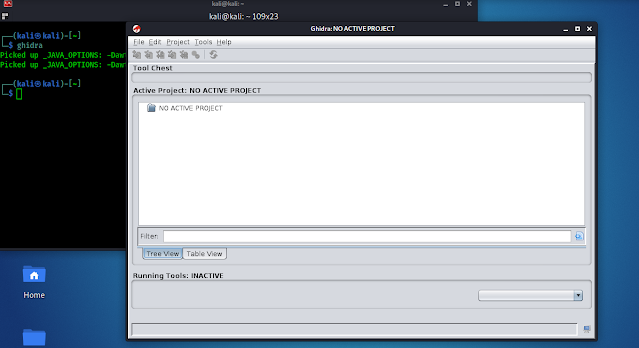
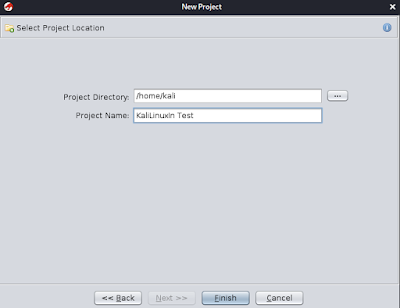
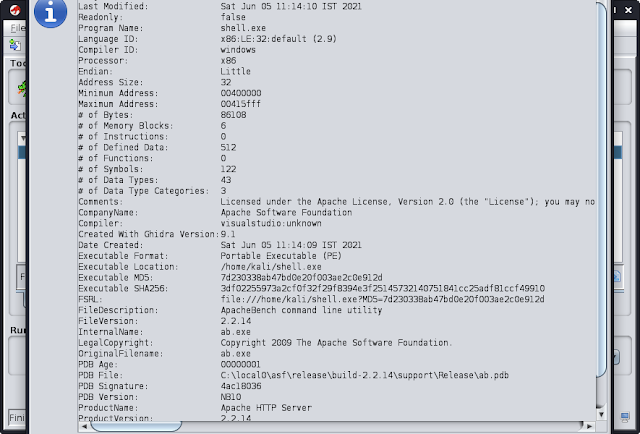
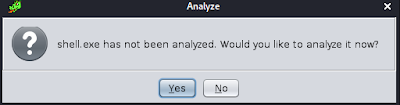
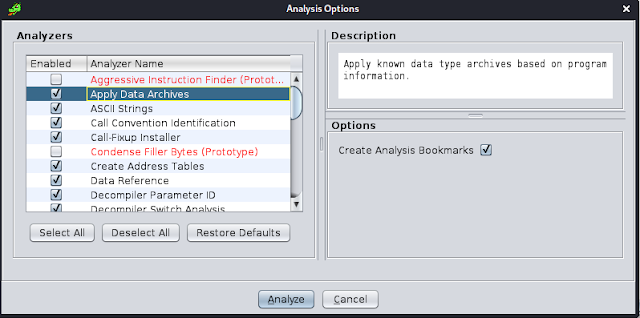
- Ghidra – Reverse engineering framework
- Pacu – AWS exploitation framework
- Peirates – Kubernetes penetration
- Quark-Engine – Android malware scoring system
- VSCode a.k.a. Visual Studio Code Open Source (“Code-OSS”) – Code editor
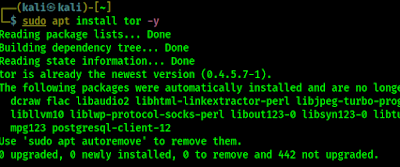
Ghidra and VSCode have been included into the kali-linux-large metapackage, so they are included on the installer image for people doing a fresh install. Otherwise you will need to upgrade Kali (if you already have the kali-linux-large install) or manually install them (if you want them!):
kali@kali:~$ sudo apt update && sudo apt install -y ghidra code-oss
A few notes about code-oss (aka VSCode):
- We are compiling this from source, rather than using the pre-built binaries
- The upside to this is that telemetry data is disabled by default
- The downside is that some aspects of the marketplace may not work. If you find these limitations a problem, you may wish to uninstall the Kali package and switch to the VSCode pre-built binaries
- You also may question why it was named
code-oss, rather than code
- Code-OSS is what the source-code calls itself, which is used as the base before the configurations are applied for the pre-compiled binaries that gets distributed as “code”
- As we are using the source-code, we used the variables defined by it
- The two different names help to distinguish the differences between them (also prevents any clashes and conflicts!)
- We also included various aliases in our package to help bridge between the two different versions. Meaning, calling
vscode and code will use our package, code-oss, with a friendly notice (when installed)
- If you already have the pre-compiled version installed, upgrading Kali will not replace it
- However, when manually installing
code-oss, it will then replace it!
Theme Enhancement
Command Line
If you are using ZSH, with the latest Kali profile applied, you can toggle between the two-line prompt and one-line prompt by pressing: CTRL + p (at the same time). This will only have an effect for the current session. If you would like to set it permanently, see kali-tweaks.
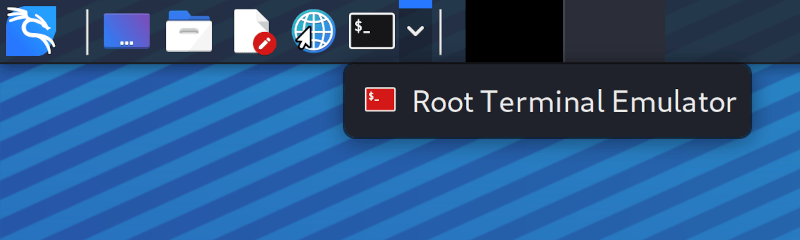
XFCE 4
We have switched up the quick launch tray in the top left, by:
- Dropping the screen recorder button (as a result package can also be removed,
kazam)
- Adding a text editor shortcut (this uses
mousepad as it is a quick and light)_
- If you are looking for something that is more substantial, try
code-oss
- Adding in a web browser icon, which starts the default browser (often
FireFox)
- Adding a drop-down menu to select the user for default terminal (
terminal or root terminal & Kali’s default is QTerminal)
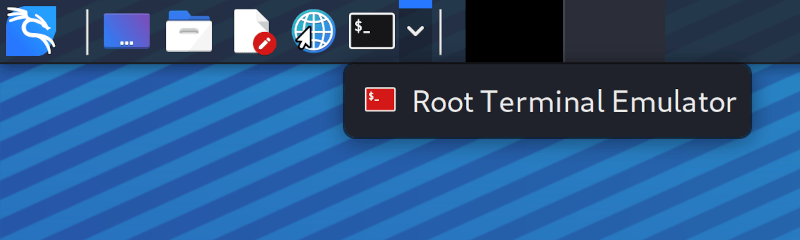
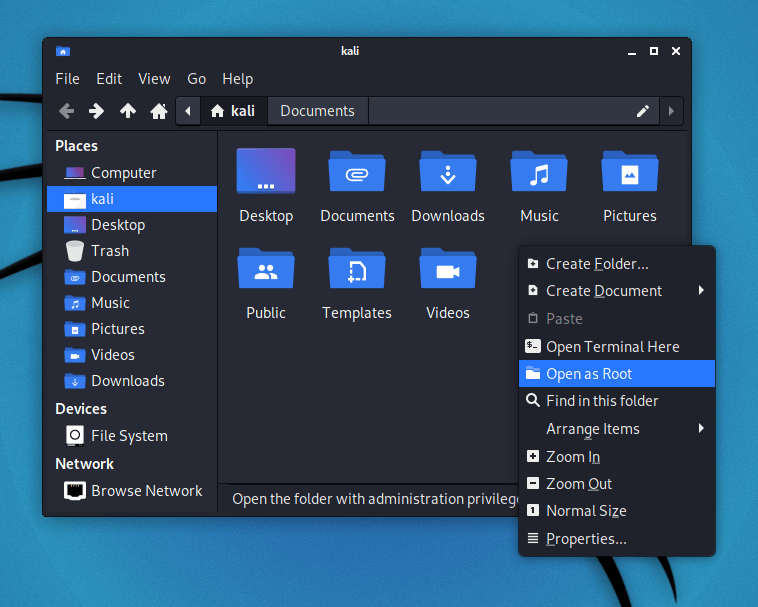
To give you an idea of how the toggling between the terminal user works:
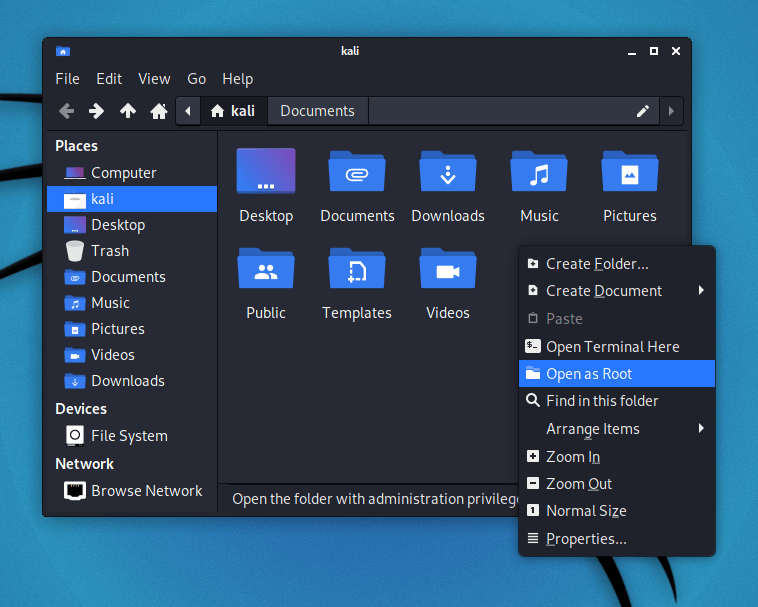
Inside of Thunar (Xfce’s default file manager), if you right-click in the main window, you should have a new option, Open as Root:
With these theme changes, you may not get them if you upgrade Kali. This is because the theme settings are copied to your home folder when your user is first created. When you upgrade Kali, it is upgrading the operating system, so upgrading does not alter personal files (just system files). As a result, in order to get these theme tweaks, you need to either:
- Do a fresh Kali install
- Create a new user and switch to that
- Delete your Xfce profile for the current user and relogin
Desktop Wallpaper & Login Background
People who have upgraded, you may have spotted that there is a new default login wallpaper and desktop background, but there are extras as well in this release:
Whilst on the subject of wallpapers, if you have not noticed, previously we had been operating on an refresh cycle about every 6 months, where we would change the default login and desktop as well as included other art work if they were not to your taste. Going forwards, we are aiming to change the defaults at every 20xx.1 release (meaning it happens right at the start of every year). So it will still change again in 6 months, but this will be the last time! We will still aim to add extra wallpapers every 6 months, however, only change the defaults yearly.
Finally, we have updated kali-community-wallpapers & kali-wallpapers-legacy packages as well!
Raspberry Pi Recharged
Two new packages:
- kalipi-config – “raspi-config on steroids” to assist in the initial setup of Kali Linux on a Raspberry Pi
- kalipi-tft-config– assist in the initial setup of TFT displays on a Raspberry Pi
And other improvements:
- Got built-in Bluetooth working on Raspberry Pi 4 & Raspberry Pi 400 (meaning all Raspberry Pi’s built-in bluetooth work!)
- This is due to
bluez, bluez-firmware , and pi-bluetooth packages forked and patched
- Raspberry Pi kernel updated to 5.4.83
- mt76 devices now work on Raspberry Pi 2 and 3 if you pass the option disable_usb_sg=1 when loading the mt76_usb module
- 1500% performance improvement
- First boot from 20 minutes to 15 seconds
- Console scrolling working
Kali NetHunter Updates
Plenty of improvements under the hood, including:
- Improved compatibility with dynamic partitions
- Improvements to persistence of Magisk root
- Improvements to Bluetooth and settings menus
- Inclusion of
rtl88xxau patches for older kernels in the kernel builder
And the highlight:
Android 11 support for:
- Nokia 6.1
- OnePlus One
- OnePlus Nord
- Xiaomi Poco F1
- Xiaomi Mi A3
- Samsung Galaxy S20 FE 5G
The Kali NetHunter repository now contains 179 kernels for 72 devices and 32 pre-built images are available on our download page
Huge thanks to @kim0coder, @yesimxev, @Svirusx, @Martinvlba, @CaliBerrr, @maade69 and the entire Kali NetHunter community for making this release happen. You absolutely rock!
More Docker support/Parallels support/Bug fixes
There are even more improvements to Kali, that are outside of the above text. Below are other note-worthy items:
- Our Kali-Docker images are now available for arm64 and armhf as well as amd64
- We have patched
pkexec, so now Qt applications which have been ran as root will maintain the dark theme and the HiDPI setting
- On a fresh Kali install,
wireshark can now be run by unprivileged users
- A couple of bugs were fixed in command-not-found, which is the terminal helper that helps you installing missing programs
- Accessibility features were not installed by default (this was a mistake on our side that is now fixed)
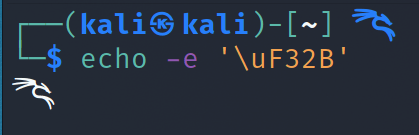
- Fixed a terminal font issue with special characters
- Apple M1 users, Parallels is no longer in “Technical Preview” and as part of the release, they’ve fixed Kali image detection.
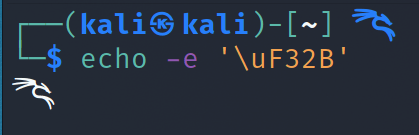
Win-KeX v2.10 has been released which now supports multiscreen- Kali’s logo is now included in the nerd-fonts project, so, with their next release you’ll be able to customize your terminal with the dragon. If you want to try it now, we’ve created a patched Fira-Code font with these new changes (the code for the logo is
uF32B)
Download Kali Linux 2021.2
Fresh Images: So what are you waiting for? Start grabbing Kali already!
Seasoned Kali Linux users are already aware of this, but for the ones who are not, we do also produce weekly builds that you can use as well. If you cannot wait for our next release and you want the latest packages (or bug fixes) when you download the image, you can just use the weekly image instead.
This way you’ll have fewer updates to do.
Just know that these are automated builds that we do not QA like we do our standard release images. But we gladly take bug reports about those images because we want any issues to be fixed before our next release!
Existing Installs: If you already have an existing Kali Linux installation, remember you can always do a quick update:
echo "deb http://http.kali.org/kali kali-rolling main non-free contrib" | sudo tee /etc/apt/sources.list
sudo apt update && sudo apt -y full-upgrade
[ -f /var/run/reboot-required ] && sudo reboot -f
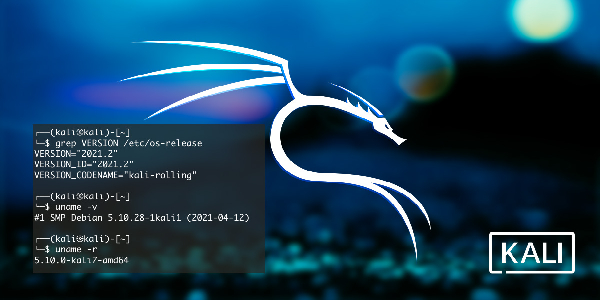
You should now be on Kali Linux 2021.2. We can do a quick check by doing:
┌──(kali㉿kali)-[~]
└─$ grep VERSION /etc/os-release
VERSION="2021.2"
VERSION_ID="2021.2"
VERSION_CODENAME="kali-rolling"
┌──(kali㉿kali)-[~]
└─$ uname -v
#1 SMP Debian 5.10.28-1kali1 (2021-04-12)
┌──(kali㉿kali)-[~]
└─$ uname -r
5.10.0-kali7-amd64
NOTE: The output of uname -r may be different depending on the system architecture.
As always, should you come across any bugs in Kali, please submit a report on our bug tracker. We’ll never be able to fix what we do not know is broken! And Twitter is not a Bug Tracker!










![Set Default Version of Python : [SOLVED] update-alternatives: error: no alternatives for python3 Set Default Version of Python : [SOLVED] update-alternatives: error: no alternatives for python3](https://infocerts.com/wp-content/uploads/2021/07/Default-Version-of-Python-infocerts.jpg)