Given a scenario, perform passive reconnaissance.
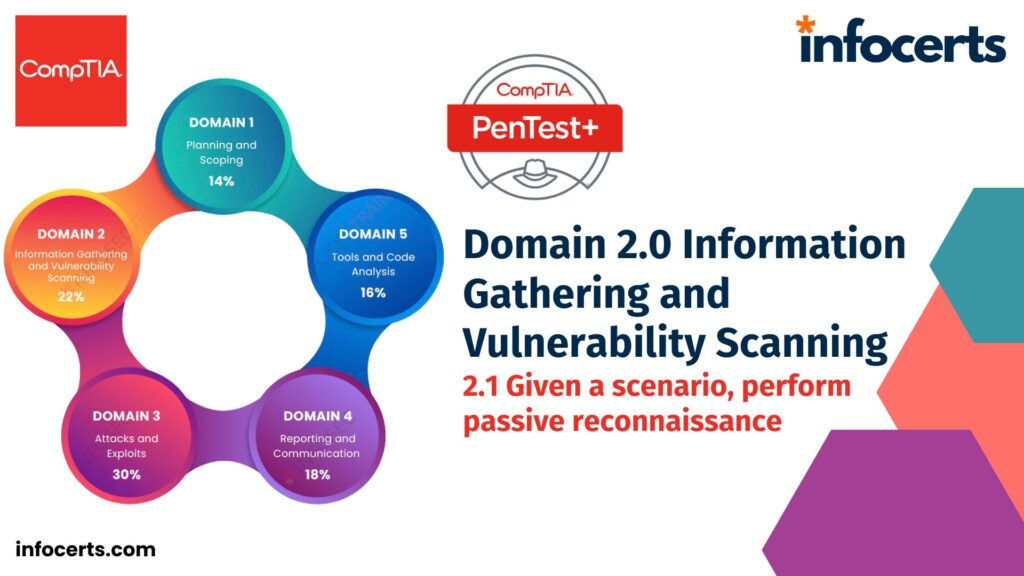
Domain 2.0 Information Gathering and Vulnerability Scanning In the world of cybersecurity, information gathering and vulnerability scanning form the foundation of successful penetration testing. This blog post will explore the intricacies of passive reconnaissance, enumeration, open-source intelligence (OSINT), website reconnaissance, and more, drawing insights from the Comptia Pentest+ certification. Passive Reconnaissance DNS Lookups Social Media …
Given a scenario, perform passive reconnaissance. Read More »